Initiate a Technical Consultation
Pearl Quant Systems facilitates high-level partnerships for the integration of algorithmic trading models and advanced financial research systems. Our Kuala Lumpur lab is organized to support sovereign funds, family offices, and institutional desks requiring rigorous quant systems architecture.
Direct Channels
Institutional Inquiries
info@pearlquantsystems.digitalKuala Lumpur Operations
+60 3 4000 0359Standard Operating Hours
Mon-Fri: 09:00 - 18:00 (MYT)
Laboratory Headquarters
Kuala Lumpur 59,
Federal Territory of Kuala Lumpur,
Malaysia
Lodge a Formal Inquiry
To ensure we route your request to the correct quantitative team, please specify the nature of your interest in our trading models or data research systems.
The Engagement Lifecycle
Security Clearance & Identification
All institutional inquiries undergo a verification process to ensure data integrity and compliance with international financial standards before deep-tier disclosure.
Architecture Alignment
Our lead analysts conduct a scoping session to determine which of our quant systems—whether mean reversion, momentum, or arbitrage—aligns with your mandate.
Operational Integration
Deployment of trading models into existing infrastructures, supported by our Kuala Lumpur 59 technical team throughout the lifecycle of the partnership.
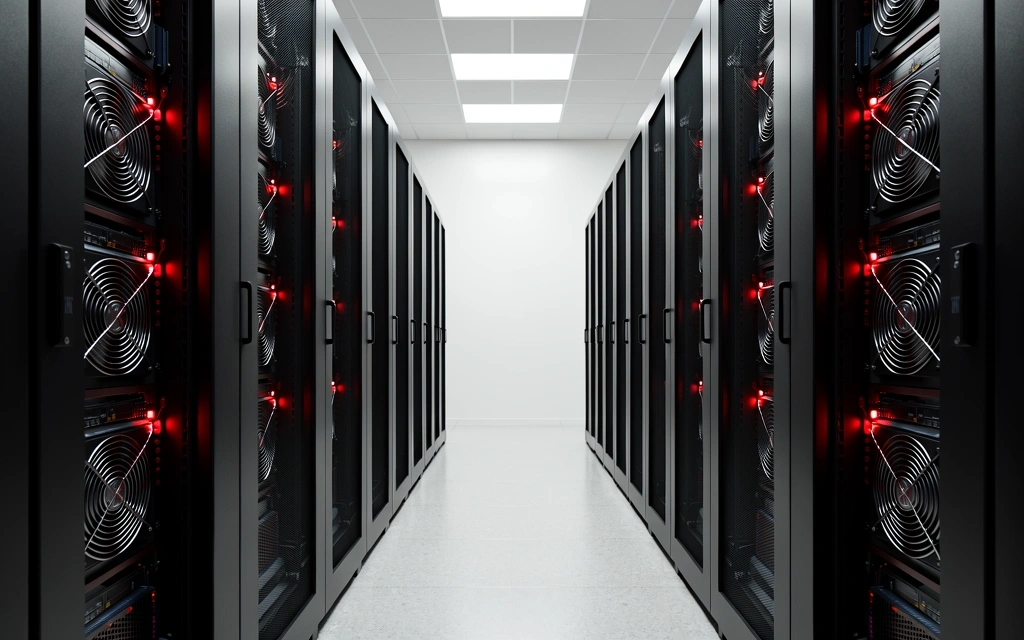
Laboratory Protocols
Operational transparency is the foundation of our trading systems. Use the resources below to understand our environment.
Response Latency
Most initial consultations are triaged within 24 standard business hours. Urgent support for existing algorithmic installations is handled through priority ticketing provided at onboarding.
Physical Access
The Kuala Lumpur lab is a secure analytical facility. Visits are strictly by appointment and require prior clearance through our security liaison department.
Data Governance
Pearl Quant Systems adheres to stringent privacy standards. All communications are encrypted and managed in accordance with our Privacy Policy.
Vendor Relations
We are currently not accepting unsolicited software vendor applications. Our technology stack is maintained through private, long-term procurement agreements.